
Project overview
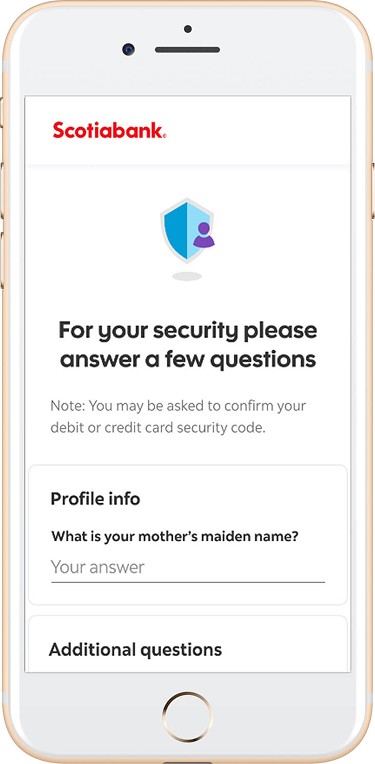
Many legacy accounts use security questions and answers to verify their identity during login to access their bank digitally (about 800,000 customers). This method of authentication verifies user’s identity by asking personal information. However, answers to these security questions can be phished, thereby making these account vulnerable to fraudsters.
Goals: Strengthen login security by replacing 2-step verification (2SV) knowledge based security questions such as “What high school did you attend” with a more secure form of authentication such as One Time Passcodes (OTP).
Platform: Mobile banking (iOS, Android) and Web (online banking)
Problem
Need for stronger security with seamless usability
Many banking fraud cases are a result of weak authentication methods. As account takeover (ATO) incidents continued to rise, it became clear that a more secure authentication method was needed. However, introducing an extra form of verification during login, a high frequency flow, risked creating frustration.
Challenge
How might we make account login safer without adding friction?
User research and insights
Insight 1: Security answers can be forgotten
Customer feedback and customer support call logs showed that many customers did not remember their security answers, especially if the questions were set years ago. In addition, customers were confused and frustrated about why they were being asked security questions.
Insight 2: Security questions can be phished
The fraud team reported multiple cases where fraudsters bypassed 2-step verification by correctly guessing or maliciously acquiring answers to security questions. This was a major vulnerability to our login flows.
Key insight
Knowledge based authentication adds risks and frustration. One Time Passcodes (OTP) was more secure and user friendly.
Call centre log review
We collaborated with the call centre operations team to review call logs related to security questions from the past 6 months.
Examples of customers’ response:
"I set those questions when I opened my account ages ago; No idea what answer I provided back then".
"How am I supposed to know how much I spent in my last transaction when I can’t access my banking app! I need to log in to get the answer".
"I cannot access my online banking. I need the 2 step verification security questions removed from my bank account immediately".
Hypothesis
Replacing these security questions with a more secure form of authentication such as 2SV Push notification or One-Time Passcode (OTP) could reduce fraud risks and improve log in success rate.
Solution
Replace security questions with One Time Passcode (OTP) 2-step verification
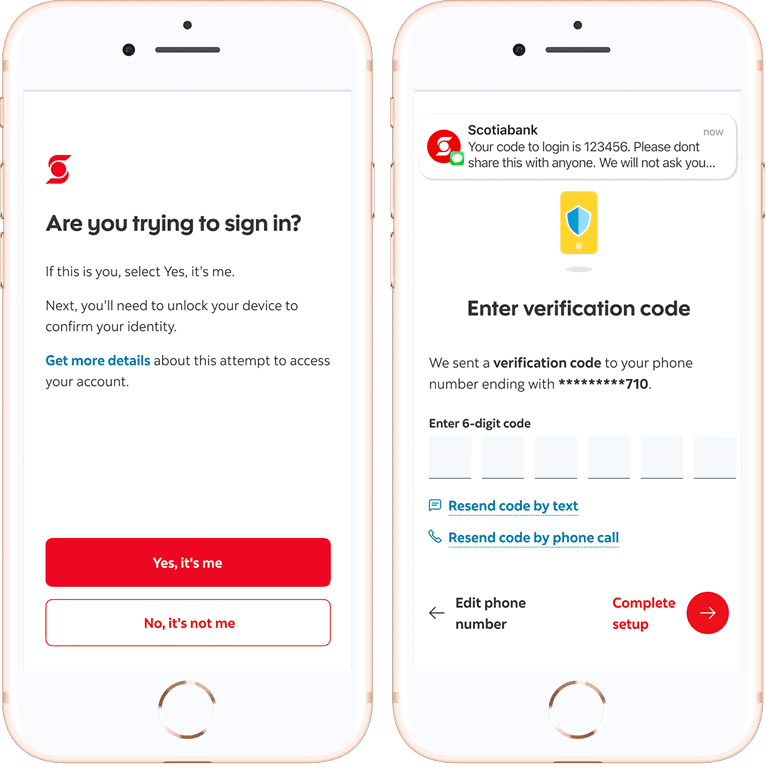
We proposed migrating every customer using security question and answer to log into their account to a more secure authentication method within four months. One Time Passcode (OTP) reduced the need for memory/knowledge based authentication and made account log in more secure and faster.
The migration would be implemented in three phases:
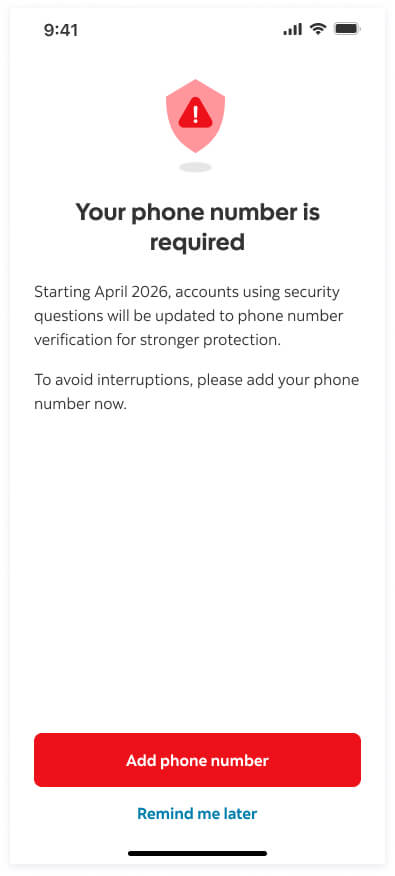
Phase 1: Include a 'skip for now' link which would make setting up one time passcode optional for customers. Intercept would be shown to customer after 3 weeks.
Phase 2: Include a 'skip for now' link which would make setting up one time passcode optional for customers. Intercept would be shown to customer after every 10 days.
Phase 3: Remove 'skip for now' link and make one time passcode enrolment a mandatory step for customers to access their digital bank account.
Rationale: Designing and shipping the changes in phases would give customers time to familiarize themselves with the incoming changes.
V1 launch
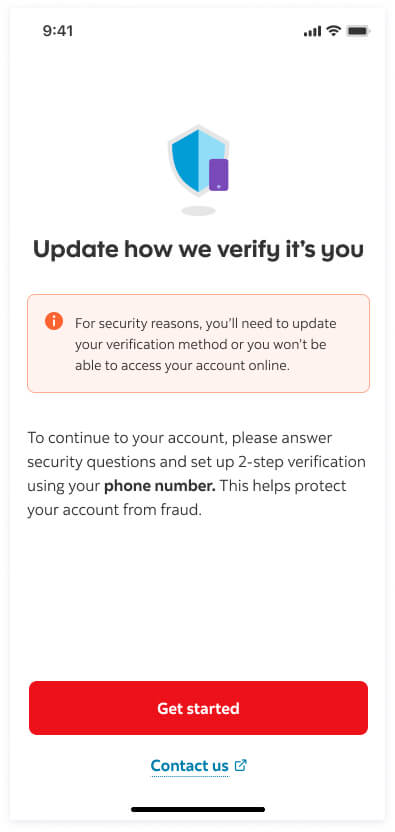
Phase 1 - Skippable 2SV enrolment intercept
In the first phase, enrolling into 2-step verification (2SV) during log in was optional. I included a 'Skip for now' link to give customers the choice of setting up 2SV immediately or deferring it to a later time.
I collaborated with our content designer to create email campaigns to communicate the new changes, benefits of 2-step verification to customers, and when/why 2SV is triggered (e.g. new device).
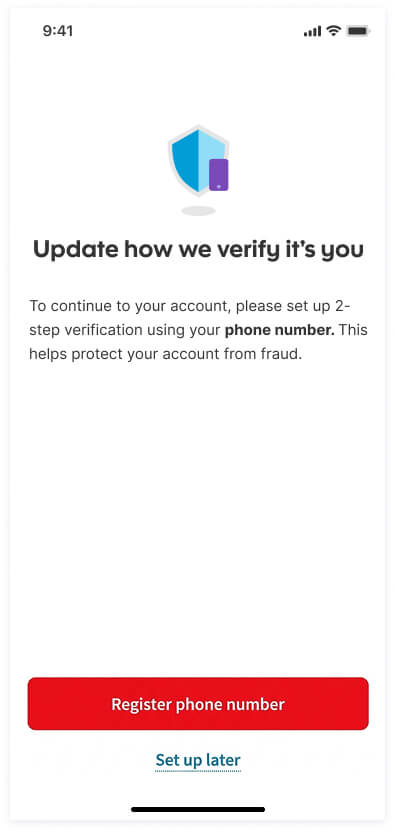
Phase 2 — Skippable 2SV enrolment intercept with increased frequency
In the second phase, similar to the first phase, enrolling into 2-step verification (2SV) during log in was optional. We increased the frequency of intercept from every 3 weeks to every 10 days and updated the copy to be more educational to educate customers on the reason to move off from security questions.
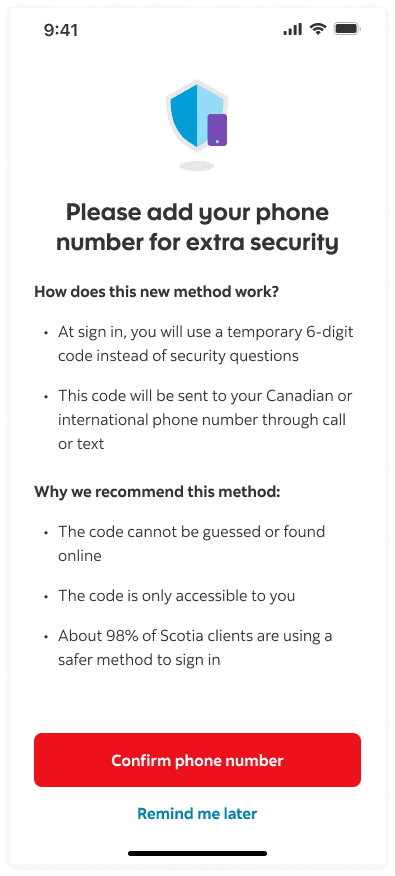
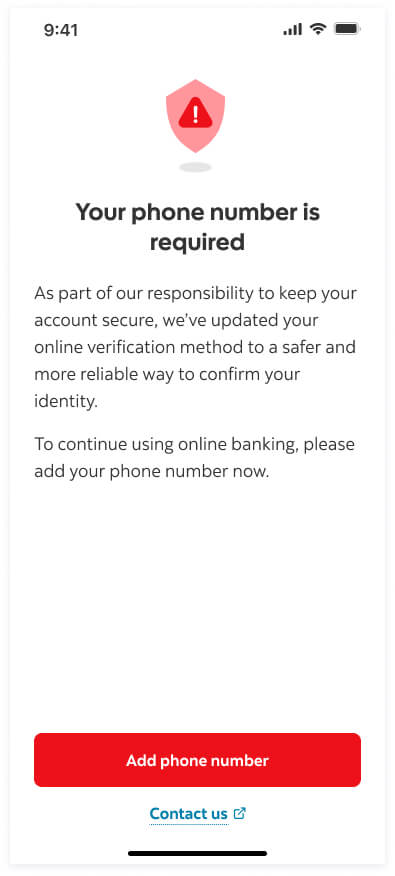
Phase 3 — Non-skippable 2SV enrolment
In the third phase, 2-step verification (2SV) enrolment became mandatory. We removed the 'Skip for now' option to ensure all customers adopted a more secure authentication method.
Customers who previously logged into the digital account using knowledge based security questions and answers were shown an intercept screen prompting them to set up 2SV One Time Passcode (OTP) before they could proceed to their online banking.
Usability testing
Listening, learning, and iterating
We saw a spike in call volumes few weeks after phase 2 rollout, customers were not happy with the mandatory 2SV enrolment. Despite extensive planning and testing, a few critical issues emerged after rollout and this impacted customer experience and prompted rapid iteration.
Call listening exercise and insights:
The design and product team regrouped to understand the spike in call volumes and get a clearer understanding of customers’ pain points. My design lead led a call listening exercise. The call centre team provided us with over 200 recent calls relating to security questions to 2SV one time passcode migration.
What we heard:
"The person reading the voice code speaks too fast. I don’t have enough time to write it down, so I have to go back to my computer to resend the code, then switch back to my phone to listen again."
"I have mobility issues and don't use a mobile phone. Every time you send a code to my landline, I have to get up and go answer it. It's not easy for me."
"How am I supposed to access my account? Not everyone has a cell phone that can receive text message."
Insights
Seniors in care homes faced barriers with voice OTPs
Customers that bank on desktop often don’t have their mobile phones nearby
Some customers don’t have SMS-capable phones
Voice One Time Passcodes are difficult to remember
Iterating based on feedback
Following insights from the call listening sessions, we made the decision to roll back the mandatory 2SV enrolment feature. Instead, we continued to support adoption through a multi-channel awareness campaign, including email, call centre scripts, and in-branch messaging, to help customers understand the benefits of having a stronger authentication and the rationale for moving away from security questions.
We also partnered with the accessibility team to improve the accessibility of the voice One Time Passcode (OTP) experience. Based on user feedback, the message was re-recorded at a slower pace to ensure that customers, including those with hearing, mobility, or cognitive challenges, could hear and write down the code without stress.
V2 launch: final solution
Phase 1 — Mass Email campaign
For the second launch, I collaborated with a content designer to design an email campaign. We sent out the emails to let customers know we were sunsetting the use of security questions as a method of authentication.
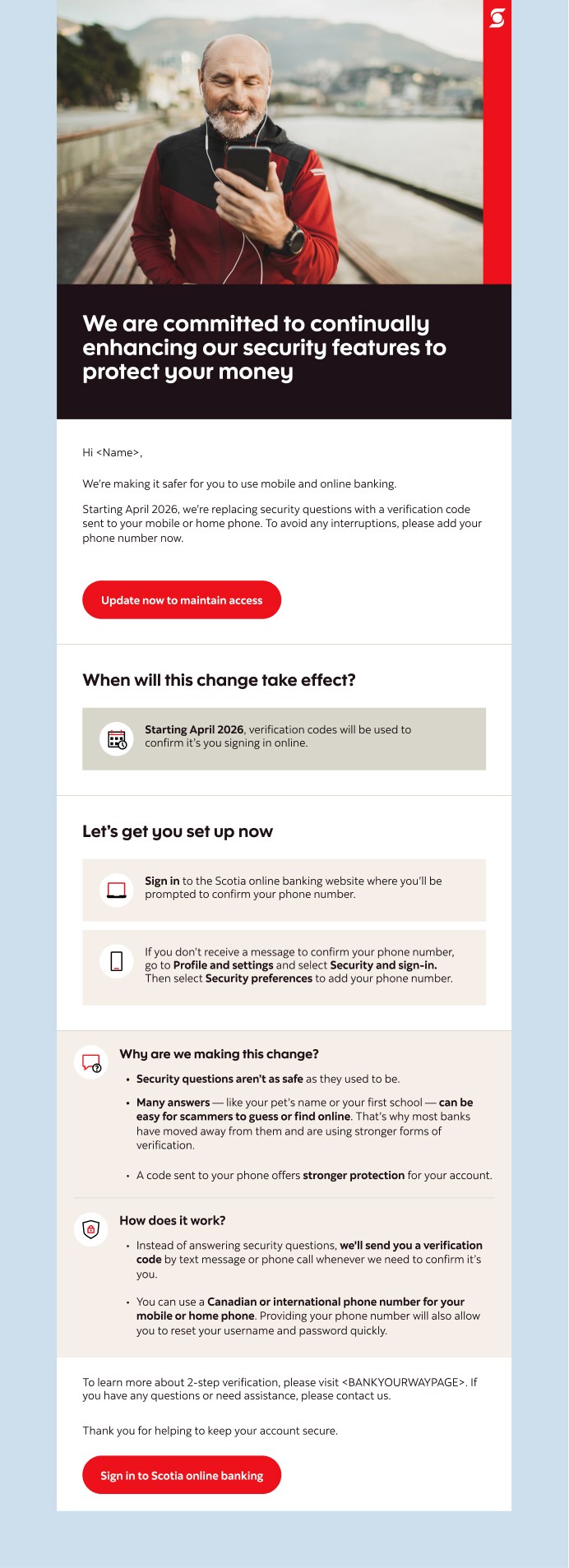
Phase 2 — Skippable intercept with more urgency
Following the mass email campaign, we launched a new intercept screen that had more urgency but supportive tone. Enrolling into 2SV during log in was optional.
Phase 3 — Non-skippable intercept
The final intercept right before the security question decommission was mandatory. At this stage, 75% of security question customers had enrolled into One Time Passcode (OTP). The content had a strict tone to let customers know that they only way to continue into online banking was to enrol into a much stronger authentication method.
Final screens
V1 launch versus V2 launch
Impact
83% increase in One Time Passcode (OTP) enrolment, showing higher adoption of secure 2-step verification practices
Reduced support call related to account lockout and 2SV confusion
Improved customer understanding of why stronger authentication matters, leading to a higher trust in the login experience
Reflections
Designing for security is not a one-size-its-all. What's simple for one customer may introduce confusion to another. This project reminded me to design with inclusivity in mind, accounting for different ages, devices, and contexts, while never compromising on safety.




